What is the issue?
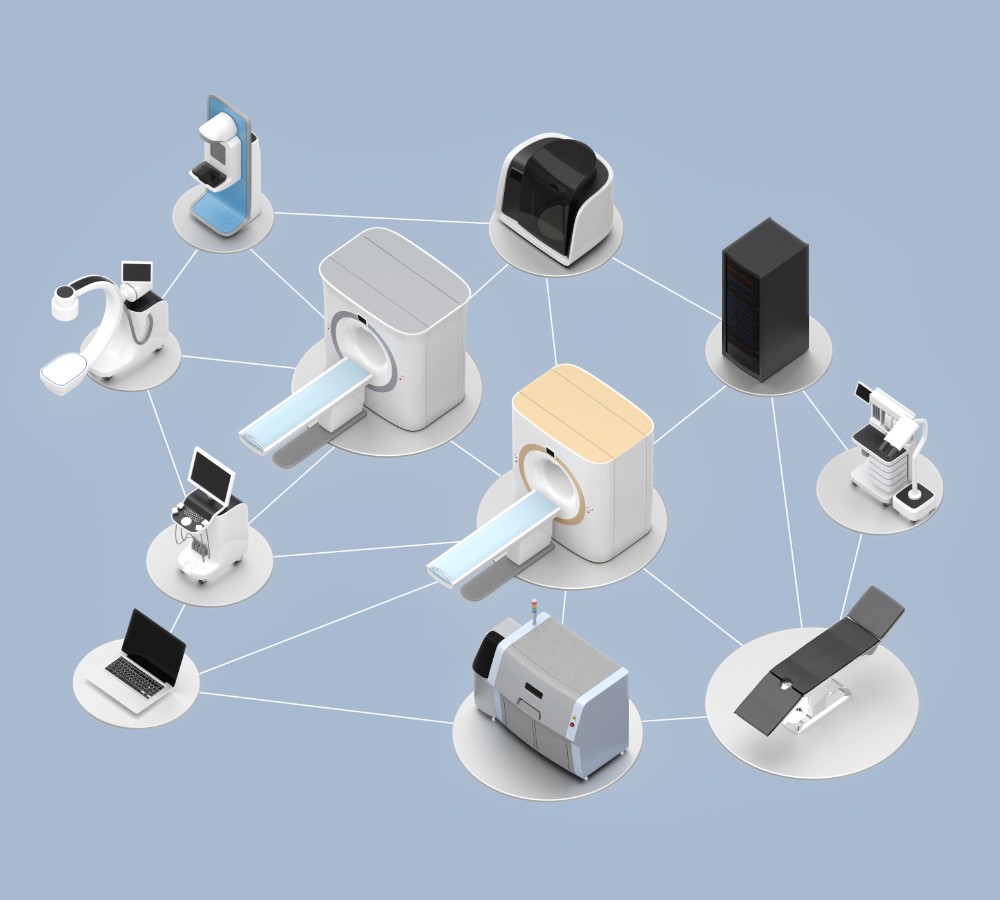
According to CSO, more than half (53%) of the IoT and internet of medical things (IoMT) devices used in healthcare contain critical cybersecurity risks, according to The State of IoMT Device Security report by Cynerio, which analysed devices from more than 300 hospitals in the US. IV pumps are the worst affected, but devices from many hospital departments were found to be running on unsupported versions of Windows or plagued by weak passwords. And that’s across 10 million connections.
Is this a priority?
Preventing unauthorised access should be a top priority for medical organisations. According to ZDNet, healthcare has become the number one target for cybercriminals in recent years, primarily due to outdated systems and not enough cybersecurity protocols. More than 93% of healthcare [organisations] experienced some type of data breach between 2016-2019. One attack in Maryland during Covid-19 saw it unable to release its statistics on the pandemic for more than a month. And that’s not an isolated case. But there are some simple steps you can take to minimise patient risk following this report.
How can you minimise patient risk?
Upgrade all related software
If the OS or integrated software can be updated through patches and security installations, then that needs to be the priority. Many manufacturers have already accounted for cyberthreats within these updates, and they simply need to be deployed to repair many of the current vulnerabilities. If devices cannot be upgraded to a point where they are enhanced with the latest security, then they need to be replaced to protect patients.
Eliminate shared passwords
More than 20% of the sampled devices were connected via shared passwords. While it might seem easier to have a single password for every device in an organisation, that’s the easiest access point for hackers. And once they’ve guessed your universal password, every single connected device is compromised. Instead, have a different secure password for every IoMT device.
Scrutinise commercially controlled devices
According to Med-tech News application-layer security protects the entire communication channel between the smartphone app, the medical device, and the cloud. It defends against a variety of malware and wireless channel cybersecurity attacks. Rather than simply rely on the lower stack levels and be subject to mobile phone operating system vulnerabilities, the application natively builds in its own security. It creates a secure tunnel between the sender and receiver. You want this with any commercially controlled IoMT device because it means that communication is encrypted and validated at each stage for a robust security protocol.